India Cybersecurity and Data Protection: Laws, Compliance, and Digital Security Framework
Introduction
India’s digital transformation has accelerated at an unprecedented pace, bringing with it both opportunities and challenges in safeguarding sensitive information and maintaining robust cybersecurity frameworks. As businesses, government entities, and individuals increasingly rely on digital platforms, the need for stringent security management and regulatory compliance has become paramount. The legal landscape governing cybersecurity and data protection in India has evolved substantially, transitioning from basic legislative provisions to sophisticated regulatory mechanisms designed to address contemporary digital threats.
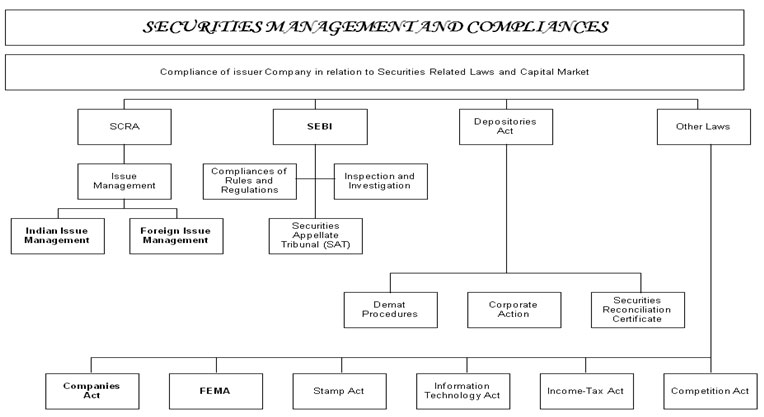
Security management and compliance in India encompasses a multifaceted approach involving statutory regulations, sectoral guidelines, judicial pronouncements, and enforcement mechanisms. This framework aims to protect critical information infrastructure, ensure data privacy, prevent cybercrimes, and establish accountability for entities handling digital information. Understanding this ecosystem requires examining the foundational legislation, regulatory bodies, compliance requirements, and landmark judicial interventions that shape how organizations operate in the digital sphere.
The Information Technology Act, 2000: Foundation of Cyber Law
The Information Technology Act, 2000 [1] serves as the cornerstone of India’s cybersecurity legal framework. Enacted by the Indian Parliament and receiving presidential assent on June 9, 2000, this legislation was India’s first comprehensive attempt to provide legal recognition to electronic transactions and address cybercrime. The Act was modeled after the United Nations Commission on International Trade Law (UNCITRAL) Model Law on Electronic Commerce, demonstrating India’s commitment to aligning with international standards.
The IT Act contains 94 sections divided into 13 chapters, covering digital signatures, electronic governance, cybersecurity, penalties, and offences related to computer systems and networks. The legislation grants legal validity to electronic records and digital signatures, establishing that contracts formed through electronic means are legally enforceable. This foundational principle enabled the growth of e-commerce and digital governance initiatives across the country.
Under Chapter IX of the Act, various penalties and compensation mechanisms were established for unauthorized access, data theft, and introduction of computer viruses. Whoever, without permission of the owner or any other person in charge of a computer system, accesses or attempts to access such computer system, downloads data, introduces computer viruses, or causes denial of access shall be liable to pay damages by way of compensation to the affected person. The penalties under this chapter can extend to one crore rupees, demonstrating the serious nature with which the law treats cyber offences.
Chapter XI of the IT Act defines specific offences and prescribes imprisonment terms for various cyber violations. Hacking, as defined under the original provisions, includes unauthorized access to computer systems with dishonest or fraudulent intent and carries punishment of imprisonment up to three years or fine extending to five lakh rupees, or both. The Act also addresses tampering with computer source code, cyber terrorism, publishing obscene material, and identity theft, each carrying specific punitive measures.
A significant amendment to the IT Act came in 2008, introducing new provisions to address emerging cyber threats. This amendment added sections dealing with identity theft, cyber terrorism, and child pornography. The amendment also established the Cyber Appellate Tribunal to handle appeals against orders of the Controller of Certifying Authorities and Adjudicating Officers, providing a specialized judicial mechanism for cyber-related disputes.
Landmark Judicial Interpretation: Shreya Singhal Case
The constitutional validity of certain provisions of the IT Act was tested in the landmark case of Shreya Singhal v. Union of India [2], decided by the Supreme Court of India on March 24, 2015. This case fundamentally altered the landscape of online free speech in India and established important precedents regarding the balance between security measures and fundamental rights.
Shreya Singhal, a law student from Delhi, filed a Public Interest Litigation challenging Section 66A of the Information Technology Act, which criminalized sending offensive messages through communication services. The provision had been widely criticized for its vague language and potential for misuse. Section 66A stated that any person who sends information that is grossly offensive or has menacing character, or causes annoyance, inconvenience, danger, obstruction, insult, injury, criminal intimidation, enmity, hatred, or ill will through a computer resource or communication device shall be punishable with imprisonment up to three years and with fine.
A two-judge bench comprising Justices J. Chelameswar and R.F. Nariman examined whether Section 66A violated Article 19(1)(a) of the Constitution, which guarantees freedom of speech and expression. The Court held that Section 66A was unconstitutional in its entirety because it arbitrarily, excessively, and disproportionately invaded the right of free speech and expression. The provision failed to satisfy the test of reasonable restrictions under Article 19(2) of the Constitution.
Justice R.F. Nariman, delivering the judgment, observed that the section was vague and overbroad, creating a chilling effect on free speech. The Court noted that expressions like “grossly offensive,” “annoyance,” and “inconvenience” were not defined and could be interpreted subjectively, leading to arbitrary application by law enforcement agencies. The judgment emphasized that for a restriction on speech to be reasonable, it must be narrowly tailored and precisely defined, which Section 66A failed to achieve.
However, the Supreme Court upheld the constitutional validity of Section 69A of the IT Act, which empowers the Central Government to block public access to information through computer resources in the interest of sovereignty, integrity, defense, security, or friendly relations with foreign states. The Court found that this section contained adequate procedural safeguards and was narrowly drawn to serve legitimate state interests.
The Shreya Singhal judgment [2] had far-reaching implications for digital rights in India. It established that online speech deserves the same constitutional protection as offline speech and that laws restricting digital expression must meet rigorous constitutional standards. This decision reinforced the principle that technological advancement cannot justify erosion of fundamental freedoms.
Constitutional Right to Privacy: The Puttaswamy Judgment
The foundation for data protection and privacy rights in India was firmly established through the nine-judge bench decision in Justice K.S. Puttaswamy (Retd.) v. Union of India [3], delivered on August 24, 2017. This landmark judgment recognized privacy as a fundamental right intrinsic to life and liberty under Article 21 of the Indian Constitution, overturning previous judicial precedents that had denied constitutional protection to privacy.
Justice K.S. Puttaswamy, a retired judge of the Karnataka High Court, challenged the constitutional validity of the Aadhaar scheme, arguing that mandatory biometric identification violated the right to privacy. The case required the Supreme Court to reconsider earlier decisions in M.P. Sharma v. Satish Chandra (1954) and Kharak Singh v. State of Uttar Pradesh (1962), which had held that privacy was not a fundamental right under the Indian Constitution.
The unanimous nine-judge bench, comprising Chief Justice J.S. Khehar and Justices J. Chelameswar, S.A. Bobde, R.K. Agrawal, R.F. Nariman, A.M. Sapre, D.Y. Chandrachud, S.K. Kaul, and S. Abdul Nazeer, held that the right to privacy is protected as an intrinsic part of the right to life and personal liberty under Article 21 and as part of the freedoms guaranteed by Part III of the Constitution. Justice D.Y. Chandrachud, writing the lead opinion, observed that privacy is the constitutional core of human dignity and includes informational privacy, bodily integrity, and decisional autonomy.
The judgment established that while privacy is a fundamental right, it is not absolute and may be subject to reasonable restrictions. However, any infringement of privacy must satisfy a three-pronged test: there must be a legitimate state interest, the means adopted must be rationally connected to the objective, and there must be proportionality between the invasion of privacy and the legitimate aim sought to be achieved. This framework created a robust standard for evaluating government actions that impact privacy.
The Puttaswamy decision [3] emphasized that informational privacy includes the right of individuals to control dissemination of personal information and the right to decide how personal data is used. The Court recognized that in the digital age, the collection, storage, and analysis of personal data pose significant risks to individual autonomy and dignity, necessitating strong legal protections. This judgment laid the groundwork for comprehensive data protection legislation in India.
Digital Personal Data Protection Act, 2023
Building upon the constitutional foundation laid by the Puttaswamy judgment, India enacted its first comprehensive data protection legislation, the Digital Personal Data Protection Act, 2023 [4], which received presidential assent on August 11, 2023. This Act represents a paradigm shift in how personal data is regulated in India, establishing clear rights for individuals and obligations for entities processing personal data.
The DPDP Act applies to processing of digital personal data within India, where such data is collected either in digital form or in non-digital form and subsequently digitized. The legislation also has extraterritorial application, covering processing of personal data outside India if it relates to offering goods or services to individuals within Indian territory. This broad jurisdictional scope ensures that foreign entities targeting Indian users must comply with Indian data protection standards.
The Act defines personal data as data about an individual who is identifiable by or in relation to such data. It introduces the concepts of Data Principal, referring to the individual to whom personal data relates, and Data Fiduciary, meaning any person who alone or in conjunction with others determines the purpose and means of processing personal data. This terminology establishes clear roles and responsibilities in data processing relationships.
A cornerstone principle of the DPDP Act is consent-based processing. Data Fiduciaries must obtain free, specific, informed, unconditional, and unambiguous consent from Data Principals before processing their personal data. The consent must be accompanied or preceded by a notice describing the personal data sought to be collected and the purpose of processing. This notice must be presented in clear and plain language, giving individuals the option to access it in English or any language specified in the Eighth Schedule to the Constitution.
The Act grants Data Principals several rights, including the right to access information about personal data processed, the right to correction and erasure of inaccurate or incomplete data, the right to nominate an individual who can exercise rights on their behalf in case of death or incapacity, and the right to grievance redressal. These rights empower individuals to exercise meaningful control over their personal information.
Data Fiduciaries bear significant obligations under the DPDP Act. They must implement appropriate technical and organizational measures to ensure compliance, maintain reasonable security safeguards to prevent personal data breaches, erase personal data once the purpose of processing is fulfilled, and notify the Data Protection Board of India and affected Data Principals of any data breach. Failure to comply with these obligations can result in substantial penalties.
The Act creates the Data Protection Board of India [4], an independent regulatory authority responsible for monitoring compliance, adjudicating violations, and imposing penalties. The Board has the power to impose fines up to 250 crore rupees for serious breaches, making it one of the most stringent data protection regimes globally in terms of potential penalties. The phased implementation approach, with compliance deadlines extending over 12-18 months, allows organizations time to align their practices with regulatory requirements.
Sectoral Regulations and Compliance Requirements
Beyond the overarching framework of the IT Act and DPDP Act, India has developed sector-specific cybersecurity regulations tailored to the unique requirements of different industries. These regulations recognize that financial institutions, healthcare providers, telecommunications companies, and other sectors face distinct security challenges requiring specialized compliance measures.
The Reserve Bank of India issued the Cybersecurity Framework for Banks in 2016 [5], mandating comprehensive cybersecurity policies for all commercial banks, urban cooperative banks, and payment system operators. This framework requires banks to establish a Cyber Security Operations Centre, appoint a Chief Information Security Officer at board or senior management level, conduct regular vulnerability assessments and penetration testing, implement robust access controls and authentication mechanisms, and maintain incident response and disaster recovery plans. Banks must report cybersecurity incidents to RBI within specified timeframes and undergo annual cybersecurity audits by empaneled auditors.
The Securities and Exchange Board of India introduced the Cybersecurity and Cyber Resilience Framework through its circular dated August 20, 2024 [6], applicable to all SEBI-regulated entities including stock exchanges, brokers, depositories, and asset management companies. This framework mandates implementation of information security policies aligned with international standards, regular security assessments, employee training programs, and establishment of Security Operations Centers. Non-compliance with SEBI cybersecurity directives can result in penalties of 20,000 rupees per day until compliance is achieved, demonstrating the regulator’s commitment to enforcing security standards.
The Department of Telecommunications has implemented stringent regulations for telecom service providers through various guidelines and the Telecommunications (Telecom Cyber Security) Rules, 2024 [7]. These rules require telecom operators to maintain transaction logs for two years, report cybersecurity incidents to CERT-In within prescribed timelines, implement network security measures including firewalls and intrusion detection systems, and ensure all telecom equipment undergoes mandatory testing and certification for security compliance. The rules reflect recognition that telecommunications infrastructure constitutes critical national infrastructure requiring heightened protection.
The Indian Computer Emergency Response Team, established under Section 70B of the IT Act, serves as the national nodal agency for responding to cybersecurity incidents. CERT-In issued comprehensive directions in April 2022 requiring service providers, intermediaries, data centers, and corporate entities to report cybersecurity incidents within six hours of noticing such incidents or being brought to notice about such incidents. Organizations must maintain logs of internet communication for 180 days, synchronize system clocks with Network Time Protocol servers, and designate points of contact for coordination with CERT-In.
Critical Information Infrastructure Protection
Recognizing that certain computer resources are vital to national security, economy, public health, and safety, the IT Act provides special protections for Critical Information Infrastructure. Section 70 of the Act empowers the Central Government to declare any computer resource as protected system, and unauthorized access to such systems constitutes a specific offence punishable with imprisonment up to ten years.
The National Critical Information Infrastructure Protection Centre was established under Section 70A to serve as the designated authority for protecting critical information infrastructure. NCIIPC has identified six critical sectors: power and energy, banking and financial services, telecommunications, transport, government and strategic public enterprises, and e-governance. Organizations operating protected systems within these sectors must comply with additional security requirements beyond general cybersecurity regulations.
The Information Technology (National Critical Information Infrastructure Protection Centre and Manner of Performing Functions and Duties) Rules, 2013 [8] specify obligations for operators of protected systems. These include appointing a Chief Information Security Officer, establishing a Cyber Security Operations Centre, conducting regular risk assessments and security audits, implementing multi-layered security controls, ensuring physical security of critical infrastructure, and maintaining detailed security documentation. The rules create a comprehensive security architecture designed to prevent, detect, and respond to sophisticated cyber threats against critical national assets.
Operators of protected systems must obtain prior approval from NCIIPC before implementing major changes to system architecture, introducing new technologies, or outsourcing critical functions. This approval mechanism ensures that security implications are thoroughly evaluated before modifications that could introduce vulnerabilities. The strict regulatory oversight reflects the recognition that compromising critical infrastructure could have cascading effects on national security and economic stability.
Enforcement Mechanisms and Penalties
The effectiveness of any regulatory framework depends on robust enforcement mechanisms. India’s cybersecurity and data protection compliance regime incorporates multiple enforcement channels including civil penalties, criminal prosecution, and regulatory sanctions. This multilayered approach ensures that violations are addressed through appropriate mechanisms based on the nature and severity of non-compliance.
The IT Act prescribes civil liability under Section 43 for unauthorized access, data theft, virus introduction, denial of service, and other specified acts that cause wrongful loss or damage. Affected persons can seek compensation up to one crore rupees from Adjudicating Officers appointed under Section 46. This civil remedy provides a relatively expeditious mechanism for victims to obtain redress without going through prolonged criminal proceedings.
Criminal offences under Chapter XI of the IT Act carry imprisonment terms ranging from three years to life imprisonment depending on the gravity of the offence. Hacking with dishonest or fraudulent intent, identity theft, cyber terrorism, and child pornography are among the serious offences attracting stringent punishment. These criminal provisions serve deterrent and retributive functions, signaling that cybercrimes will be punished severely.
The DPDP Act introduces a graduated penalty structure based on the nature of violation. Data Fiduciaries failing to implement reasonable security safeguards or breaching obligations related to children’s data face penalties up to 200 crore rupees. Failure to provide information to the Data Protection Board or non-compliance with Board directions attracts penalties up to 250 crore rupees. This substantial penalty regime creates strong financial incentives for compliance.
Sectoral regulators like RBI and SEBI impose additional penalties for violations of sector-specific cybersecurity requirements. RBI can impose monetary penalties on banks under the Banking Regulation Act for inadequate cybersecurity controls. SEBI’s enforcement powers include suspension of operations, cancellation of registration, and monetary penalties. The multiplicity of enforcement authorities ensures comprehensive oversight across different sectors.
Challenges in Implementation and Compliance
Despite the comprehensive legal framework, India faces several challenges in effectively implementing cybersecurity and data protection regulations and ensuring widespread compliance. The rapidly evolving nature of cyber threats, technological complexity, resource constraints, and awareness gaps pose significant obstacles to achieving the desired level of cybersecurity maturity across organizations.
Many small and medium enterprises lack the technical expertise and financial resources to implement sophisticated cybersecurity measures mandated by regulations. The cost of hiring qualified cybersecurity professionals, deploying advanced security technologies, and conducting regular audits can be prohibitive for smaller organizations. This creates a compliance gap where regulatory requirements exist on paper but are not effectively implemented in practice.
The shortage of skilled cybersecurity professionals in India exacerbates compliance challenges. Organizations struggle to recruit and retain qualified Chief Information Security Officers, security analysts, and incident response personnel. Educational institutions have been slow to develop curricula that address contemporary cybersecurity needs, resulting in a talent pipeline that cannot meet industry demand. Addressing this skills gap requires coordinated efforts among government, industry, and academia.
Awareness and understanding of compliance requirements remain uneven across organizations. Many entities, particularly in traditional sectors undergoing digital transformation, lack clear understanding of their obligations under the IT Act, DPDP Act, and sectoral regulations. The absence of comprehensive implementation guidance and best practices contributes to confusion about compliance expectations. Regulatory authorities need to enhance their outreach and education efforts to bridge this knowledge gap.
The enforcement infrastructure, while improving, faces capacity constraints. The number of Adjudicating Officers under the IT Act and the resources available to the Data Protection Board may be insufficient to handle the volume of complaints and violations in a timely manner. Delays in enforcement can undermine the credibility of the regulatory regime and reduce deterrence. Strengthening enforcement capacity requires sustained investment in institutional infrastructure.
Conclusion
Security management and compliance in India has evolved from nascent legislative provisions to a sophisticated regulatory ecosystem encompassing statutory frameworks, sectoral regulations, constitutional protections, and enforcement mechanisms. The Information Technology Act, 2000 established the foundational legal architecture, while subsequent amendments and complementary legislation like the Digital Personal Data Protection Act, 2023 have adapted the framework to address emerging challenges in the digital age.
Landmark judicial pronouncements, particularly Shreya Singhal v. Union of India and Justice K.S. Puttaswamy v. Union of India, have shaped the constitutional contours of cybersecurity regulation, ensuring that security measures respect fundamental rights to free speech and privacy. These judgments demonstrate the judiciary’s crucial role in balancing security imperatives with individual liberties in a democratic society.
The sectoral approach to cybersecurity regulation, with specialized requirements for banking, securities markets, telecommunications, and critical infrastructure, recognizes that different domains face unique threats and require tailored security measures. This nuanced regulatory strategy allows for flexibility while maintaining robust protection standards across the economy. Organizations operating in India must navigate this complex compliance landscape, implementing appropriate security controls while adhering to sector-specific mandates.
Looking forward, India’s cybersecurity regulatory framework will need to continue evolving to address emerging technologies like artificial intelligence, blockchain, and Internet of Things, which present novel security challenges. The successful implementation of the DPDP Act will be crucial in establishing India as a jurisdiction with strong data protection standards. Continued focus on enforcement capacity, awareness building, and skills development will determine the effectiveness of this comprehensive legal architecture in creating a secure digital ecosystem for India’s growing digital economy.
References
[1] The Information Technology Act, 2000 (No. 21 of 2000), Act of Parliament of India, June 9, 2000. Available at: https://www.indiacode.nic.in/handle/123456789/1999
[2] Shreya Singhal v. Union of India, AIR 2015 SC 1523, Writ Petition (Criminal) No. 167 of 2012, Supreme Court of India, March 24, 2015. Available at: https://indiankanoon.org/doc/110813550/
[3] Justice K.S. Puttaswamy (Retd.) and Anr. v. Union of India and Ors., Writ Petition (Civil) No. 494 of 2012, Supreme Court of India, August 24, 2017. Available at: https://indiankanoon.org/doc/91938676/
[4] The Digital Personal Data Protection Act, 2023 (No. 22 of 2023), Act of Parliament of India, August 11, 2023. Available at: https://www.meity.gov.in/writereaddata/files/Digital%20Personal%20Data%20Protection%20Act%202023.pdf
[5] Reserve Bank of India, “Cyber Security Framework in Banks,” June 2, 2016. Available at: https://iclg.com/practice-areas/cybersecurity-laws-and-regulations/india
[6] Securities and Exchange Board of India, “Cybersecurity and Cyber Resilience Framework (CSCRF) for SEBI Regulated Entities (REs),” Circular No. SEBI/HO/ITD-1/ITD_CSC_EXT/P/CIR/2024/113, August 20, 2024. Available at: https://www.cyberlawconsulting.com/cybersecurity_regulations_india_2024.php
[7] Telecommunications (Telecom Cyber Security) Rules, 2024, Ministry of Communications, Government of India. Available at: https://www.cyberlawconsulting.com/cybersecurity_regulations_india_2024.php
[8] Information Technology (National Critical Information Infrastructure Protection Centre and Manner of Performing Functions and Duties) Rules, 2013. Available at: https://www.lexology.com/library/detail.aspx?g=d599eba2-e69a-4121-95b4-ff84e49730c6
[9] Ministry of Electronics and Information Technology, “Digital Personal Data Protection Rules, 2025,” Press Information Bureau, November 14, 2025. Available at: https://www.pib.gov.in/PressReleasePage.aspx?PRID=2190655
 Whatsapp
Whatsapp